Identifying Malicious DNS Tunnel Tools from DoH Traffic Using Hierarchical Machine Learning Classification | SpringerLink

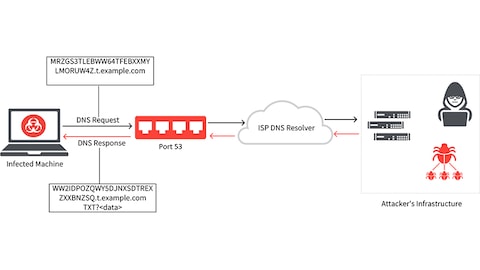
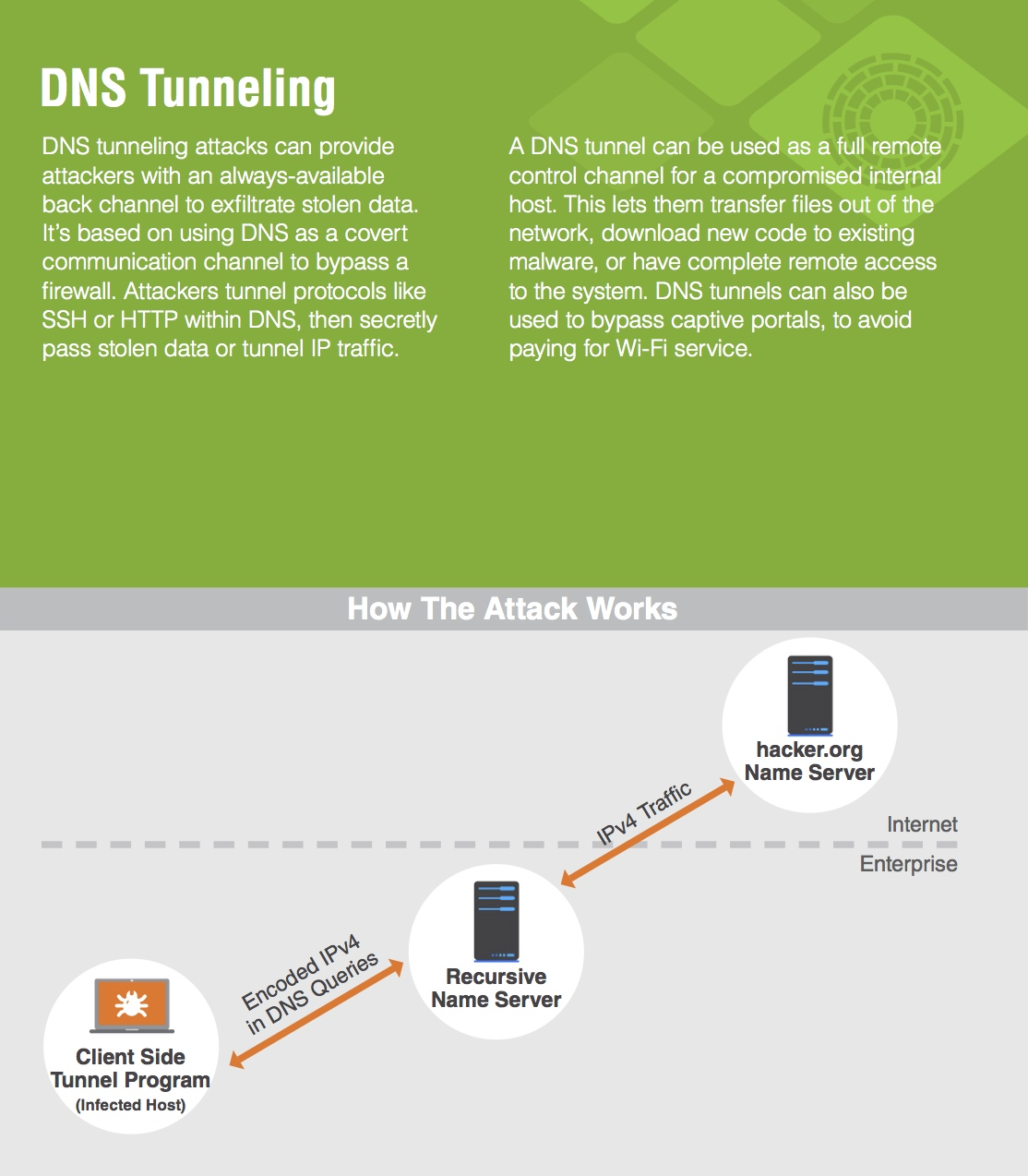
Detect DNS Tunneling done by tools such as iodine with ELK stack + Packetbeat and Watcher : r/netsec
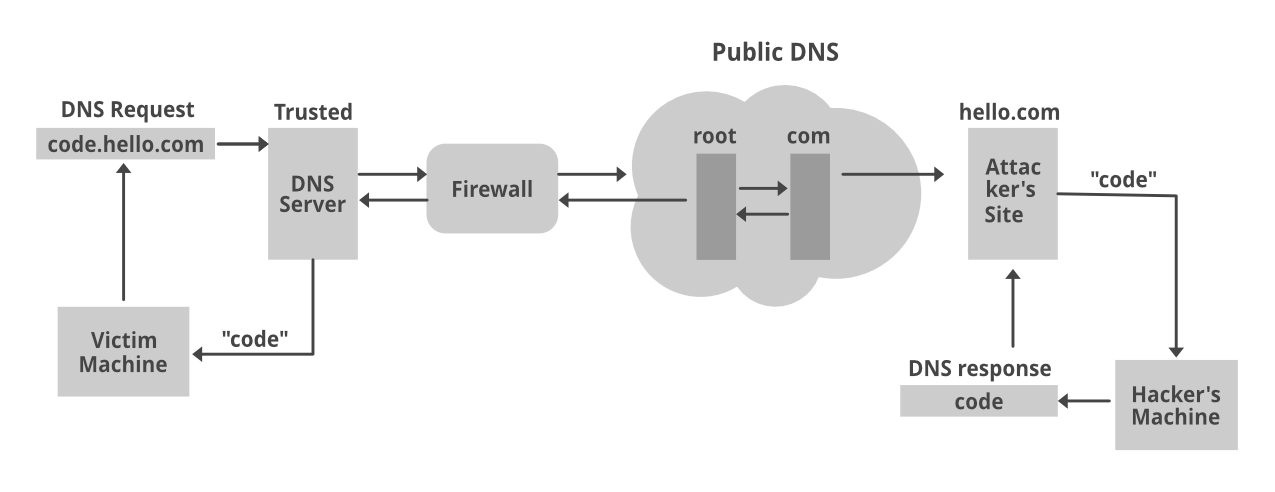
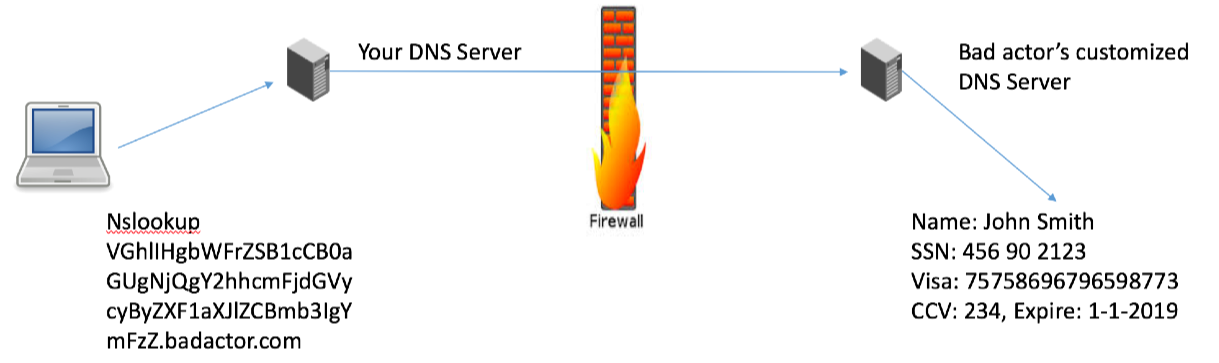
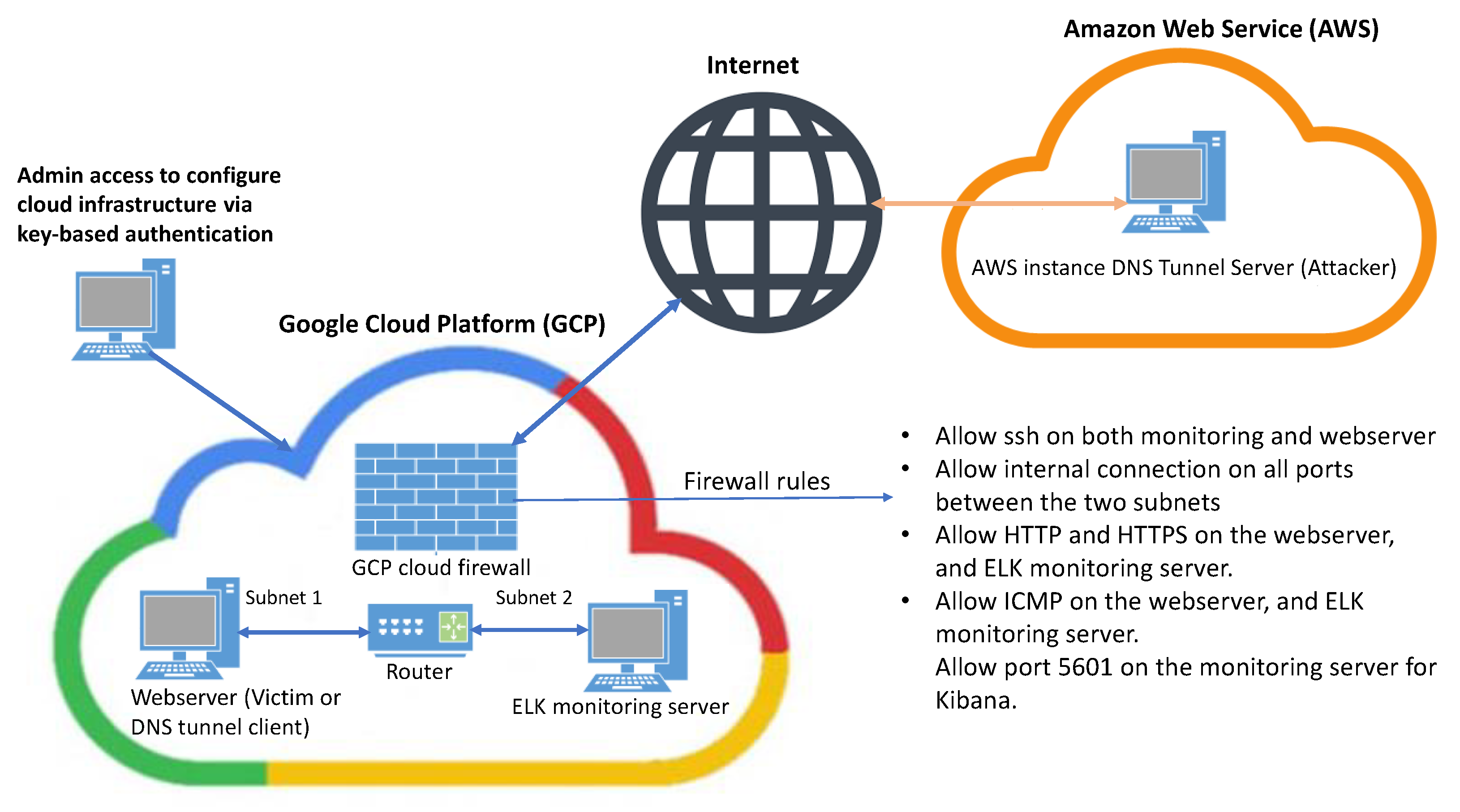
DNS Tunneling Simulation Topology 3.1. Log aggregation and simulation.... | Download Scientific Diagram
![PDF] Behavior Analysis based DNS Tunneling Detection and Classification with Big Data Technologies | Semantic Scholar PDF] Behavior Analysis based DNS Tunneling Detection and Classification with Big Data Technologies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/b7bc7d2eb9c0f18b5e0e5da3cc6903acfe7c29fe/1-Figure1-1.png)